Key Goals of DEPS and Project overview
Key Goals of DEPS
The research proposed by DEPS is characterized by the following goals:
- Seek transformative scientific change with broad intellectual merit by opening new research direction, namely the comprehensive protection of industrial production systems against reverse-engineering.
- Seek transformative societal change by integrating companies into the research effort to accelerate technology transfer and leverage the discovered research results to gain a competitive edge with the potential to protect market share in existing and open up new markets.
- Enable successful exploitation and marketing of obtained results through development of a suitable patent portfolio.
Project overview
DEPS proposes to break new ground by uniting software diversity with physically-unclonable functions to protect intellectual property of software deployed on embedded, robotic, and production systems in a comprehensive and cost effective, ideally cost-neutral, manner.
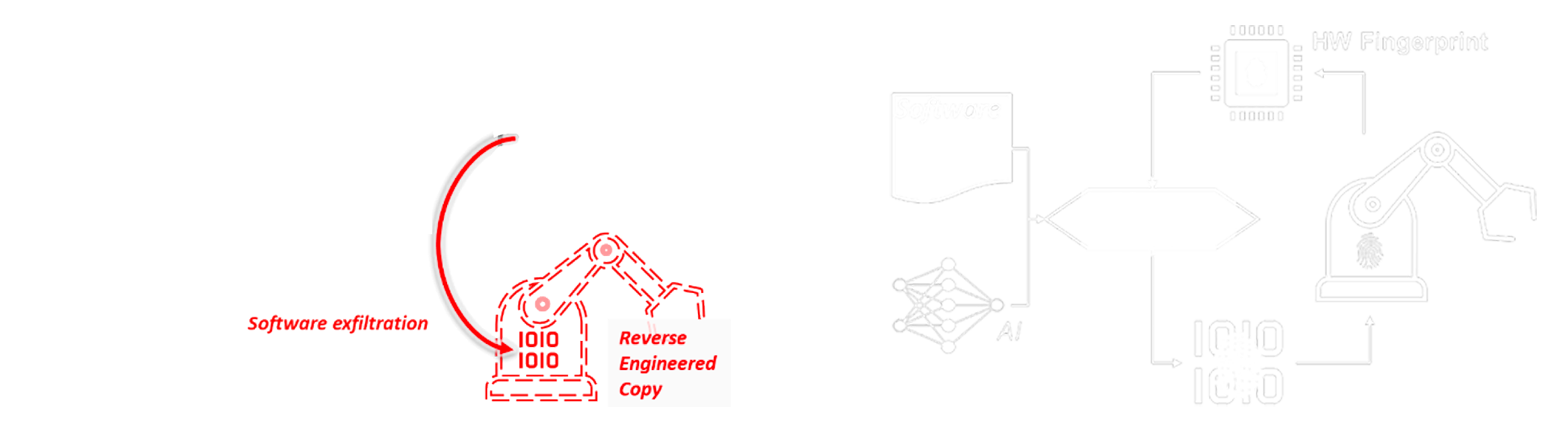
In the current situation the software is compiled to an executable binary representation of the software. Copies of this binary are then deployed on the hardware devices, so every hardware instance has the same software binary installed. In this scenario, the software may be protected with different mechanisms as outlined above. However, once a successful attack has been found, it compromises every binary instance of the software and therefore all hardware devices. In addition, illegal copies of the software can be distributed as they run on each of the hardware instances.
The envisioned solution of DEPS addresses these weaknesses in two ways. First, the idea is to overcome the inherent software monoculture by generating diverse binary instances of the same software. This can be achieved with a protection compiler (PC) that produces different binary representations yet with the same functional behavior from the original program P. These different software instances cannot be compromised by replicating the same attacks, so a single successful attack on one instance has less impact on the entire ecosystem. In addition, the generation of different binaries can also include and combine protection methods like tamper proofing and obfuscation for an enhanced combined protection that is customized to each individual instance.
The second part of the approach is about hardware identification. The software running on the hardware is able to identify the hardware instance where it runs by unique properties of the hardware system. The vision is to enable this identification without additional hardware support. The hardware properties can be tied into the program logic like array access or similar. This tight integration prevents the detection and makes it very difficult to circumvent. Therefore, the software can be made to only work correctly on the related hardware and illegal copies of the software are rendered useless.
The combination of both mechanisms together provide a comprehensive protection for industrial software
- It securely binds the software to unique hardware properties and therefore provides effective copy protection without additional hardware extensions.
- The combination of diverse binaries with tamper proofing and obfuscation as well as the binding to hardware properties provides effective protection of the protection mechanisms themselves.
- Optimized software generation and direct integration of protection methods in the software should avoid expensive outbound communication, key management or encryption of the software.
- Automated analysis, generation and deployment of the software makes the protection approach applicable for mass production.
- Updates to hardware and/or software require re-compilation of the software for the specific target hardware. However, these tasks can be automated with hardware/software management.
This protection is of key importance to maintain economic sovereignty and resilience for European companies and governments alike, supporting the European action plan1. If successful, the research proposed by DEPS opens up a new research direction that increases in importance and relevance along with the increasing proliferation of IoT devices and advanced manufacturing and Industry 4.0 systems.